Security risk analysis template for meaningful use, For companies to survive, especially during tough economic times, they need to set themselves apart from their opponents. Innovation, therefore, becomes a key part of their success. Innovation requires a strategic vision on the part of businesses, in addition to creating conditions which can be achieved through internal modifications and progress. This can be accomplished through a procedure called Business Analysis. Business Evaluation can be described as a study into the operations of a venture directed at understanding every facet of how the enterprise is functioning including its procedures, people and performance, as well as its goals and objectives. Business Analysis is the key initial step in the program consulting procedure because it identifies enterprise wants and helps construct the services necessary to meet these needs.
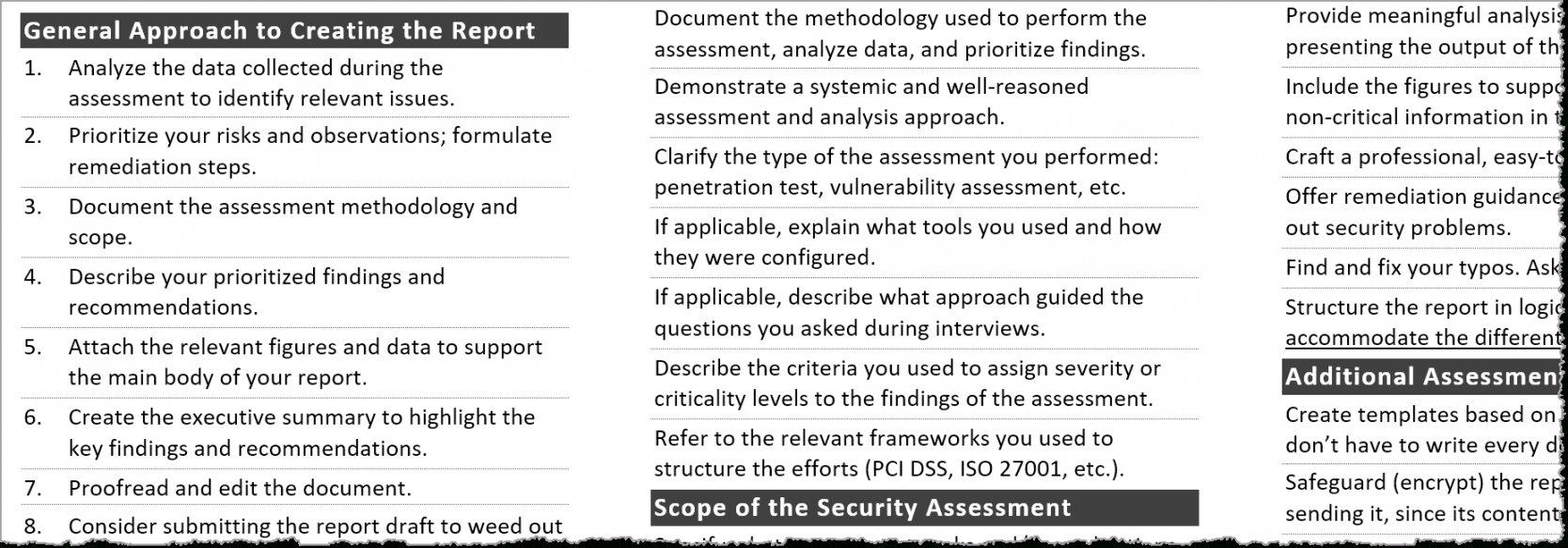
Business investigation can include market research analysis such as analyzing consumer data from these sources as transaction records, consumer surveys, surveys. . .etc. Additionally, it may have financial analysis, inventory analysis, product and service analysis, and even more. Effective small business analysis helps a company avoid making incorrect decisions which may lead to money and time being wasted when moving back to fix any problems in addition to finding the proper solution. The result of locating the right solution first time is projects get completed in a timely manner, strategies are executed with the results benefiting the organization, and there’s effective monitoring of the job which permits the best alterations that ends in the ideal outcome.
Successful business analysis permits managers to ensure accurate information is distributed and understood by the whole project team. With the right information, the staff is able to work in an efficient way to create a plan that has a better chance of succeeding. Today, there is effective business analysis software and applications that allows managers to not only keep up with current consumer purchasing trends as well as predict future trends. For instance, a supermarket that analyses and tracks customer buys are going to have the ability to design and implement advertising strategies around their customers’ personal shopping habits. As well, data from polls is another illustration of analyzing the information to ascertain the best approach to market products and services.
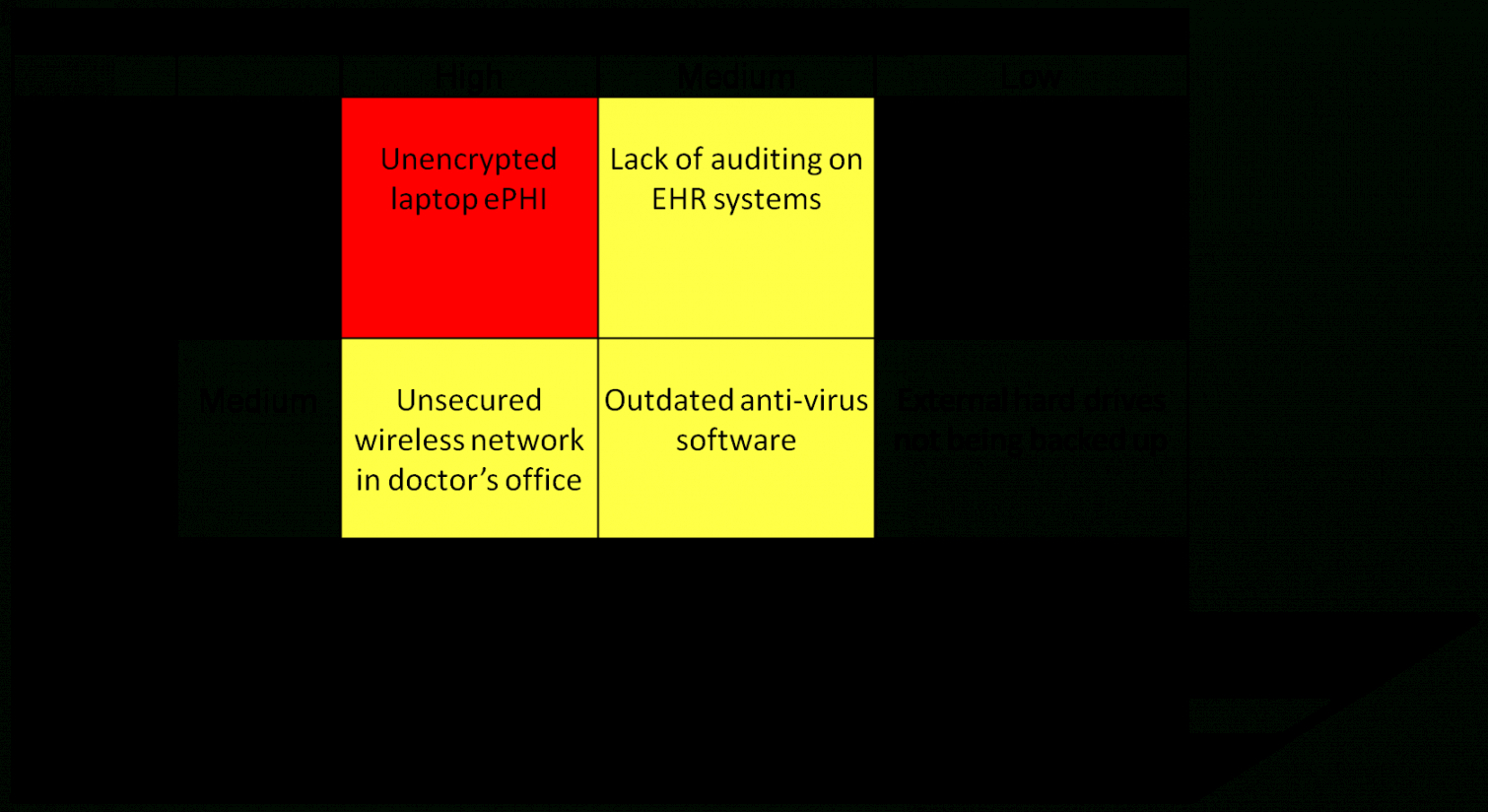
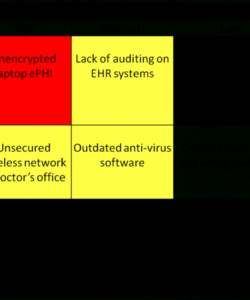
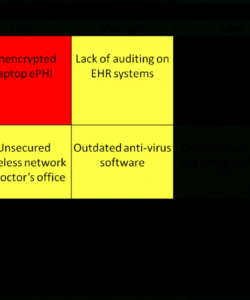
Business evaluation methods can be implemented to create a suitable plan that’s risk free and ensures stability in operations. Typically there are a great deal of dangers to manage and this is where business knowledge comes in handy. Thus it’s necessary for a company to consider and be quite sure of the project prior to going into the job. Thus it is very important to consider the pros and cons to get rid of the possibility of failures. An effective Business Analyst helps you to take control over your company and reap the benefits at low expenditure. He is an important asset to an organization as with no taking major decisions of the company would be impossible.

![Free Competitive Analysis Templates 40 Great Examples [Excel Word Pdf Ppt] Competitor Analysis Matrix Template PDF free competitive analysis templates 40 great examples [excel word pdf ppt] competitor analysis matrix template pdf](https://dremelmicro.com/wp-content/uploads/2022/08/free-competitive-analysis-templates-40-great-examples-excel-word-pdf-ppt-competitor-analysis-matrix-template-pdf-250x300.jpg)